Sign Out and Sign in Again With a Different Azure Active Directory User Account.
This browser is no longer supported.
Upgrade to Microsoft Edge to take advantage of the latest features, security updates, and technical support.
Many organizations desire to let users sign in to Azure Active Directory (Azure Advertising) using the same credentials as their on-bounds directory environment. With this approach, known as hybrid authentication, users only demand to recollect one set up of credentials.
Some organizations haven't moved to hybrid hallmark for the post-obit reasons:
- By default, the Azure Advertisement User Principal Name (UPN) is prepare to the same value equally the on-premises UPN.
- Changing the Azure AD UPN creates a mismatch between on-bounds and Azure AD environments that could cause issues with sure applications and services.
- Due to business organisation or compliance reasons, the organisation doesn't want to use the on-bounds UPN to sign in to Azure AD.
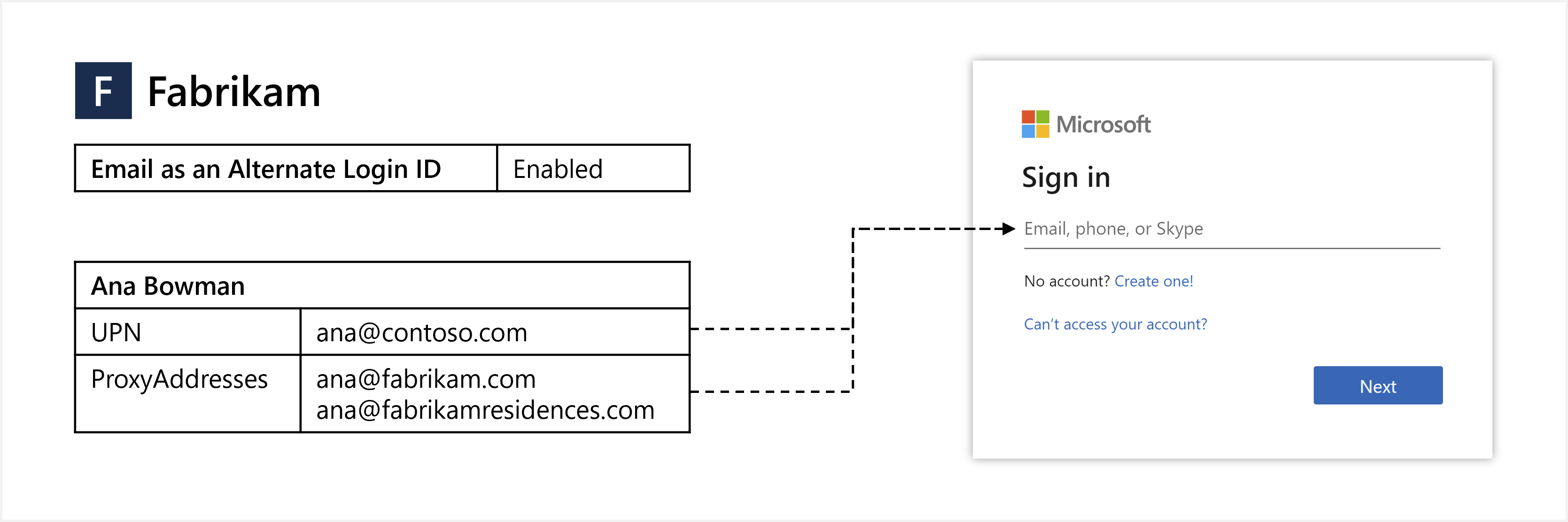
To help with the move to hybrid authentication, y'all can configure Azure AD to let users sign in with their e-mail equally an alternate login ID. For example, if Contoso rebranded to Fabrikam, rather than continuing to sign in with the legacy ana@contoso.com UPN, e-mail as an alternating login ID tin be used. To access an awarding or service, users would sign in to Azure AD using their not-UPN email, such as ana@fabrikam.com.
This commodity shows you how to enable and use email as an alternate login ID.
Before yous begin
Here's what you lot demand to know about e-mail as an alternate login ID:
- The feature is available in Azure AD Free edition and college.
- The feature enables sign-in with ProxyAddresses, in addition to UPN, for deject-authenticated Azure AD users. More on how this applies to Azure AD B2B scenarios in the B2B section.
- When a user signs in with a non-UPN e-mail, the
unique_nameandpreferred_usernameclaims (if present) in the ID token volition return the non-UPN email. - The feature supports managed authentication with Countersign Hash Sync (PHS) or Pass-Through Authentication (PTA).
- There are two options for configuring the characteristic:
- Home Realm Discovery (HRD) policy - Use this option to enable the feature for the entire tenant. Global administrator privileges required.
- Staged rollout policy - Employ this pick to test the feature with specific Azure Advertizing groups. Global ambassador privileges required.
Preview limitations
In the electric current preview state, the following limitations apply to email as an alternating login ID:
-
User experience - Users may see their UPN, even when they signed-in with their non-UPN email. The following example behavior may exist seen:
- User is prompted to sign in with UPN when directed to Azure AD sign-in with
login_hint=<non-UPN email>. - When a user signs-in with a non-UPN email and enters an incorrect countersign, the "Enter your password" page changes to display the UPN.
- On some Microsoft sites and apps, such as Microsoft Office, the Account Manager control typically displayed in the upper right may display the user's UPN instead of the non-UPN email used to sign in.
- User is prompted to sign in with UPN when directed to Azure AD sign-in with
-
Unsupported flows - Some flows are currently not uniform with not-UPN emails, such as the following:
- Identity Protection doesn't friction match non-UPN emails with Leaked Credentials take chances detection. This risk detection uses the UPN to lucifer credentials that have been leaked. For more than information, see Azure Advertisement Identity Protection risk detection and remediation.
- When a user is signed-in with a non-UPN electronic mail, they cannot change their password. Azure AD self-service password reset (SSPR) should work every bit expected. During SSPR, the user may see their UPN if they verify their identity using a non-UPN email.
-
Unsupported scenarios - The following scenarios are not supported. Sign-in with non-UPN electronic mail for:
- Hybrid Azure AD joined devices
- Azure AD joined devices
- Azure AD registered devices
- Applications using Resource Owner Password Credentials (ROPC)
- Applications using legacy hallmark such equally POP3 and SMTP
- Skype for Business
- Microsoft Part on macOS
- Microsoft 365 Admin Portal
-
Unsupported apps - Some 3rd-party applications may not work every bit expected if they presume that the
unique_nameorpreferred_usernameclaims are immutable or will always match a specific user attribute, such as UPN. -
Logging - Changes made to the feature's configuration in HRD policy are not explicitly shown in the audit logs. In addition, the Sign-in identifier blazon field in the sign-in logs may non be always accurate and should non be used to determine whether the feature has been used for sign-in.
-
Staged rollout policy - The following limitations employ only when the feature is enabled using staged rollout policy:
- The characteristic does non work equally expected for users that are included in other staged rollout policies.
- Staged rollout policy supports a maximum of ten groups per feature.
- Staged rollout policy does not back up nested groups.
- Staged rollout policy does non support dynamic groups.
- Contact objects inside the group will block the group from being added to a staged rollout policy.
-
Duplicate values - Within a tenant, a cloud-merely user's UPN can be the same value equally another user's proxy address synced from the on-premises directory. In this scenario, with the feature enabled, the cloud-just user will not be able to sign in with their UPN. More on this issue in the Troubleshoot section.
Overview of alternating login ID options
To sign in to Azure AD, users enter a value that uniquely identifies their account. Historically, you lot could just use the Azure Advertizement UPN as the sign-in identifier.
For organizations where the on-premises UPN is the user'due south preferred sign-in email, this approach was great. Those organizations would set the Azure AD UPN to the exact same value every bit the on-premises UPN, and users would have a consistent sign-in experience.
Alternate Login ID for AD FS
However, in some organizations the on-premises UPN isn't used as a sign-in identifier. In the on-premises environments, you would configure the local Ad DS to permit sign-in with an alternate login ID. Setting the Azure Advertizement UPN to the aforementioned value as the on-premises UPN isn't an pick equally Azure AD would then require users to sign in with that value.
Alternate Login ID in Azure Advertizement Connect
The typical workaround to this issue was to set the Azure AD UPN to the email address the user expects to sign in with. This approach works, though results in unlike UPNs betwixt the on-bounds Ad and Azure AD, and this configuration isn't compatible with all Microsoft 365 workloads.
Email as an Alternate Login ID
A different approach is to synchronize the Azure Advertising and on-bounds UPNs to the same value and then configure Azure Advertizement to allow users to sign in to Azure Advert with a verified electronic mail. To provide this ability, y'all define one or more e-mail addresses in the user's ProxyAddresses attribute in the on-premises directory. ProxyAddresses are then synchronized to Azure Advertisement automatically using Azure Advertizement Connect.
| Choice | Description |
|---|---|
| Alternate Login ID for AD FS | Enable sign-in with an alternate attribute (such as Postal service) for AD FS users. |
| Alternate Login ID in Azure AD Connect | Synchronize an alternating attribute (such as Post) equally the Azure Ad UPN. |
| Email as an Alternate Login ID | Enable sign-in with verified domain ProxyAddresses for Azure Advertising users. |
Synchronize sign-in email addresses to Azure AD
Traditional Active Directory Domain Services (AD DS) or Active Directory Federation Services (Ad FS) authentication happens directly on your network and is handled by your Advertisement DS infrastructure. With hybrid authentication, users tin can instead sign in directly to Azure Advert.
To support this hybrid authentication approach, you synchronize your on-premises AD DS surround to Azure Advertizement using Azure Advertisement Connect and configure it to utilize PHS or PTA. For more information, come across Choose the correct authentication method for your Azure AD hybrid identity solution.
In both configuration options, the user submits their username and countersign to Azure Advertizement, which validates the credentials and issues a ticket. When users sign in to Azure AD, information technology removes the need for your arrangement to host and manage an AD FS infrastructure.
One of the user attributes that'due south automatically synchronized by Azure AD Connect is ProxyAddresses. If users have an email address divers in the on-prem Advertisement DS environs every bit part of the ProxyAddresses aspect, it's automatically synchronized to Azure Advertising. This email address tin so be used direct in the Azure AD sign-in process every bit an alternating login ID.
Of import
Merely emails in verified domains for the tenant are synchronized to Azure AD. Each Azure AD tenant has one or more verified domains, for which yous have proven buying, and are uniquely jump to you tenant.
For more information, see Add together and verify a custom domain name in Azure AD.
B2B invitee user sign-in with an electronic mail address

Electronic mail as an alternate login ID applies to Azure AD business-to-business organization (B2B) collaboration under a "bring your own sign-in identifiers" model. When email every bit an alternate login ID is enabled in the home tenant, Azure Advertizing users can perform invitee sign in with non-UPN email on the resources tenanted endpoint. No activity is required from the resources tenant to enable this functionality.
Enable user sign-in with an e-mail address
One time users with the ProxyAddresses attribute applied are synchronized to Azure AD using Azure AD Connect, you need to enable the feature for users to sign in with email as an alternate login ID for your tenant. This characteristic tells the Azure Advertizing login servers to not only check the sign-in identifier confronting UPN values, simply likewise against ProxyAddresses values for the email address.
During preview, you tin currently only enable the sign-in with e-mail as an alternate login ID feature using PowerShell. You need global administrator permissions to complete the post-obit steps:
-
Open a PowerShell session as an administrator, then install the AzureADPreview module using the Install-Module cmdlet:
Install-Module AzureADPreviewIf prompted, select Y to install NuGet or to install from an untrusted repository.
-
Sign in to your Azure Advertisement tenant as a global ambassador using the Connect-AzureAD cmdlet:
Connect-AzureADThe control returns data well-nigh your account, surround, and tenant ID.
-
Check if the HomeRealmDiscoveryPolicy already exists in your tenant using the Get-AzureADPolicy cmdlet as follows:
Get-AzureADPolicy | Where-Object Type -eq "HomeRealmDiscoveryPolicy" | Format-List * -
If in that location'due south no policy currently configured, the command returns nothing. If a policy is returned, skip this step and move on to the adjacent footstep to update an existing policy.
To add the HomeRealmDiscoveryPolicy policy to the tenant, use the New-AzureADPolicy cmdlet and set the AlternateIdLogin aspect to "Enabled": true as shown in the post-obit example:
$AzureADPolicyDefinition = @( @{ "HomeRealmDiscoveryPolicy" = @{ "AlternateIdLogin" = @{ "Enabled" = $true } } } | ConvertTo-JSON -Compress ) $AzureADPolicyParameters = @{ Definition = $AzureADPolicyDefinition DisplayName = "BasicAutoAccelerationPolicy" IsOrganizationDefault = $truthful Type = "HomeRealmDiscoveryPolicy" } New-AzureADPolicy @AzureADPolicyParametersWhen the policy has been successfully created, the control returns the policy ID, as shown in the post-obit case output:
Id DisplayName Type IsOrganizationDefault -- ----------- ---- --------------------- 5de3afbe-4b7a-4b33-86b0-7bbe308db7f7 BasicAutoAccelerationPolicy HomeRealmDiscoveryPolicy True -
If at that place's already a configured policy, cheque if theAlternateIdLogin aspect is enabled, as shown in the post-obit example policy output:
Id : 5de3afbe-4b7a-4b33-86b0-7bbe308db7f7 OdataType : AlternativeIdentifier : Definition : {{"HomeRealmDiscoveryPolicy" :{"AlternateIdLogin":{"Enabled": true}}}} DisplayName : BasicAutoAccelerationPolicy IsOrganizationDefault : True KeyCredentials : {} Type : HomeRealmDiscoveryPolicyIf the policy exists but the AlternateIdLogin aspect that isn't nowadays or enabled, or if other attributes exist on the policy you wish to preserve, update the existing policy using the Set-AzureADPolicy cmdlet.
Important
When you update the policy, make sure you include any old settings and the newAlternateIdLogin attribute.
The post-obit case adds theAlternateIdLogin aspect and preserves theAllowCloudPasswordValidation attribute that may have already been fix:
$AzureADPolicyDefinition = @( @{ "HomeRealmDiscoveryPolicy" = @{ "AllowCloudPasswordValidation" = $truthful "AlternateIdLogin" = @{ "Enabled" = $true } } } | ConvertTo-JSON -Compress ) $AzureADPolicyParameters = @{ ID = "b581c39c-8fe3-4bb5-b53d-ea3de05abb4b" Definition = $AzureADPolicyDefinition DisplayName = "BasicAutoAccelerationPolicy" IsOrganizationDefault = $true Type = "HomeRealmDiscoveryPolicy" } Set-AzureADPolicy @AzureADPolicyParametersConfirm that the updated policy shows your changes and that the AlternateIdLogin attribute is now enabled:
Get-AzureADPolicy | Where-Object Type -eq "HomeRealmDiscoveryPolicy" | Format-List *
With the policy applied, it can take upwardly to one 60 minutes to propagate and for users to be able to sign in using their alternating login ID.
Enable staged rollout to test user sign-in with an electronic mail address
Staged rollout policy allows tenant administrators to enable features for specific Azure AD groups. It is recommended that tenant administrators employ staged rollout to examination user sign-in with an email address. When administrators are ready to deploy this feature to their entire tenant, they should use HRD policy.
You lot need global ambassador permissions to complete the following steps:
-
Open up a PowerShell session as an ambassador, then install the AzureADPreview module using the Install-Module cmdlet:
Install-Module AzureADPreviewIf prompted, select Y to install NuGet or to install from an untrusted repository.
-
Sign in to your Azure Advert tenant as a global administrator using the Connect-AzureAD cmdlet:
Connect-AzureADThe control returns data about your account, environment, and tenant ID.
-
List all existing staged rollout policies using the post-obit cmdlet:
Get-AzureADMSFeatureRolloutPolicy -
If in that location are no existing staged rollout policies for this feature, create a new staged rollout policy and accept note of the policy ID:
$AzureADMSFeatureRolloutPolicy = @{ Feature = "EmailAsAlternateId" DisplayName = "EmailAsAlternateId Rollout Policy" IsEnabled = $true } New-AzureADMSFeatureRolloutPolicy @AzureADMSFeatureRolloutPolicy -
Observe the directoryObject ID for the group to exist added to the staged rollout policy. Annotation the value returned for the Id parameter, because it will be used in the adjacent step.
Get-AzureADMSGroup -SearchString "Proper name of group to be added to the staged rollout policy" -
Add together the group to the staged rollout policy as shown in the following example. Replace the value in the -Id parameter with the value returned for the policy ID in step 4 and replace the value in the -RefObjectId parameter with the Id noted in footstep 5. It may take up to 1 60 minutes earlier users in the grouping can sign in to Azure Advertizement with email as an alternate login ID.
Add-AzureADMSFeatureRolloutPolicyDirectoryObject -Id "ROLLOUT_POLICY_ID" -RefObjectId "GROUP_OBJECT_ID"
For new members added to the group, it may take up to 24 hours before they can sign in to Azure AD with email as an alternate login ID.
Removing groups
To remove a grouping from a staged rollout policy, run the post-obit command:
Remove-AzureADMSFeatureRolloutPolicyDirectoryObject -Id "ROLLOUT_POLICY_ID" -ObjectId "GROUP_OBJECT_ID" Removing policies
To remove a staged rollout policy, first disable the policy then remove it from the system:
Set-AzureADMSFeatureRolloutPolicy -Id "ROLLOUT_POLICY_ID" -IsEnabled $false Remove-AzureADMSFeatureRolloutPolicy -Id "ROLLOUT_POLICY_ID" Examination user sign-in with an email address
To examination that users can sign in with email, go to https://myprofile.microsoft.com and sign in with a non-UPN electronic mail, such as balas@fabrikam.com. The sign-in experience should await and feel the same every bit signing-in with the UPN.
Troubleshoot
If users accept trouble signing in with their email accost, review the following troubleshooting steps:
-
Make sure it'south been at least ane hour since email as an alternate login ID was enabled. If the user was recently added to a group for staged rollout policy, make sure it'south been at least 24 hours since they were added to the group.
-
If using HRD policy, ostend that the Azure Advertizing HomeRealmDiscoveryPolicy has the AlternateIdLogin definition property set to "Enabled": true and the IsOrganizationDefault holding set to True:
Get-AzureADPolicy | Where-Object Type -eq "HomeRealmDiscoveryPolicy" | Format-List *If using staged rollout policy, ostend that the Azure Advertizing FeatureRolloutPolicy has the IsEnabled property set to True:
Become-AzureADMSFeatureRolloutPolicy -
Make sure the user account has their electronic mail address set in the ProxyAddresses attribute in Azure AD.
Alien values between cloud-only and synced users
Within a tenant, a cloud-only user's UPN may take on the aforementioned value equally another user'due south proxy accost synced from the on-premises directory. In this scenario, with the feature enabled, the cloud-just user will not be able to sign in with their UPN. Here are the steps for detecting instances of this issue.
-
Open a PowerShell session as an ambassador, then install the AzureADPreview module using the Install-Module cmdlet:
Install-Module AzureADPreviewIf prompted, select Y to install NuGet or to install from an untrusted repository.
-
Sign in to your Azure AD tenant every bit a global administrator using the Connect-AzureAD cmdlet:
Connect-AzureAD -
Get afflicted users.
# Get all users $allUsers = Get-AzureADUser -All $truthful # Become listing of proxy addresses from all synced users $syncedProxyAddresses = $allUsers | Where-Object {$_.ImmutableId} | Select-Object -ExpandProperty ProxyAddresses | ForEach-Object {$_ -Replace "smtp:", ""} # Get list of user chief names from all deject-but users $cloudOnlyUserPrincipalNames = $allUsers | Where-Object {!$_.ImmutableId} | Select-Object -ExpandProperty UserPrincipalName # Get intersection of two lists $duplicateValues = $syncedProxyAddresses | Where-Object {$cloudOnlyUserPrincipalNames -Contains $_} -
To output afflicted users:
# Output affected synced users $allUsers | Where-Object {$_.ImmutableId -And ($_.ProxyAddresses | Where-Object {($duplicateValues | ForEach-Object {"smtp:$_"}) -Contains $_}).Length -GT 0} | Select-Object ObjectId, DisplayName, UserPrincipalName, ProxyAddresses, ImmutableId, UserType # Output affected deject-just users $allUsers | Where-Object {!$_.ImmutableId -And $duplicateValues -Contains $_.UserPrincipalName} | Select-Object ObjectId, DisplayName, UserPrincipalName, ProxyAddresses, ImmutableId, UserType -
To output afflicted users to CSV:
# Output affected users to CSV $allUsers | Where-Object { ($_.ImmutableId -And ($_.ProxyAddresses | Where-Object {($duplicateValues | ForEach-Object {"smtp:$_"}) -Contains $_}).Length -GT 0) -Or (!$_.ImmutableId -And $duplicateValues -Contains $_.UserPrincipalName) } | Select-Object ObjectId, DisplayName, UserPrincipalName, @{north="ProxyAddresses"; e={$_.ProxyAddresses -Join ','}}, @{n="IsSyncedUser"; e={$_.ImmutableId.Length -GT 0}}, UserType | Export-Csv -Path .\AffectedUsers.csv -NoTypeInformation
Next steps
To learn more about hybrid identity, such as Azure Advertizement App Proxy or Azure Advertizement Domain Services, see Azure Advertizement hybrid identity for admission and management of on-prem workloads.
For more than data on hybrid identity operations, come across how countersign hash sync or pass-through authentication synchronization work.
Feedback
Submit and view feedback for
Source: https://docs.microsoft.com/en-us/azure/active-directory/authentication/howto-authentication-use-email-signin
0 Response to "Sign Out and Sign in Again With a Different Azure Active Directory User Account."
Postar um comentário